97+ pages challenges of maintaining information security at a remote recovery location 2.8mb. Minimum APA formatting guidelines. I recommend your initial posting to be between 200-to-300 words. All initial posts must contain. Check also: maintaining and understand more manual guide in challenges of maintaining information security at a remote recovery location Discuss the challenges of maintaining information security at a remote recovery location.
Dont use plagiarized sources. Note that the requirement is to post your initial response no later than Sunday and you must post one additional post during the week.
Pdf Reviewing Cyber Security Social Engineering Training And Awareness Programs Pitfalls And Ongoing Issues
| Title: Pdf Reviewing Cyber Security Social Engineering Training And Awareness Programs Pitfalls And Ongoing Issues |
| Format: PDF |
| Number of Pages: 330 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: June 2017 |
| File Size: 2.6mb |
| Read Pdf Reviewing Cyber Security Social Engineering Training And Awareness Programs Pitfalls And Ongoing Issues |
 |
Discuss the challenges of maintaining information security at a remote recovery location.
The replies to fellow students and to the professor should range between 100-to-150 words. Even though Information security is important there are lots of challenges in maintaining information security at remote recovery location. All initial posts must contain a properly formatted in-text citation and scholarly reference. Even though Information security is important there are lots of challenges in maintaining information security at remote recovery location. All initial posts must contain a properly formatted in-text citation and scholarly reference. All initial posts must contain a properly formatted in-text citation and scholarly reference.
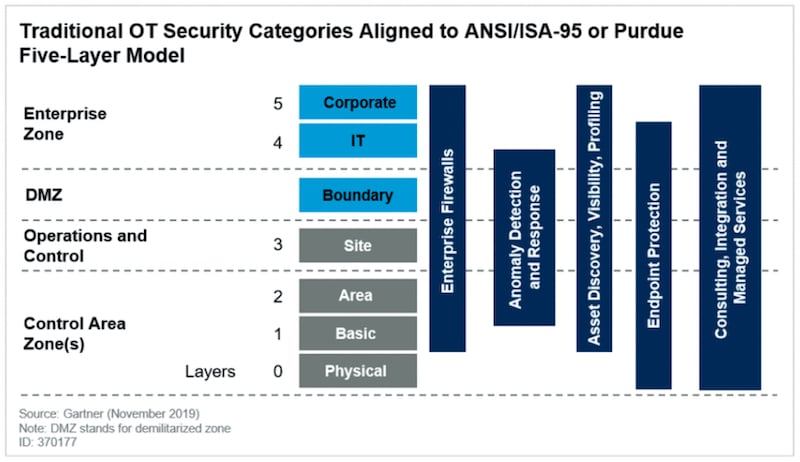
Cybersecurity Ot A Prehensive Guide
| Title: Cybersecurity Ot A Prehensive Guide |
| Format: eBook |
| Number of Pages: 313 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: December 2019 |
| File Size: 6mb |
| Read Cybersecurity Ot A Prehensive Guide |
 |
S Sparta Eu Assets Deliverables Sparta D9 1 Cybersecurity Skills Framework Pu M12 Pdf
| Title: S Sparta Eu Assets Deliverables Sparta D9 1 Cybersecurity Skills Framework Pu M12 Pdf |
| Format: eBook |
| Number of Pages: 188 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: June 2021 |
| File Size: 1.6mb |
| Read S Sparta Eu Assets Deliverables Sparta D9 1 Cybersecurity Skills Framework Pu M12 Pdf |
 |
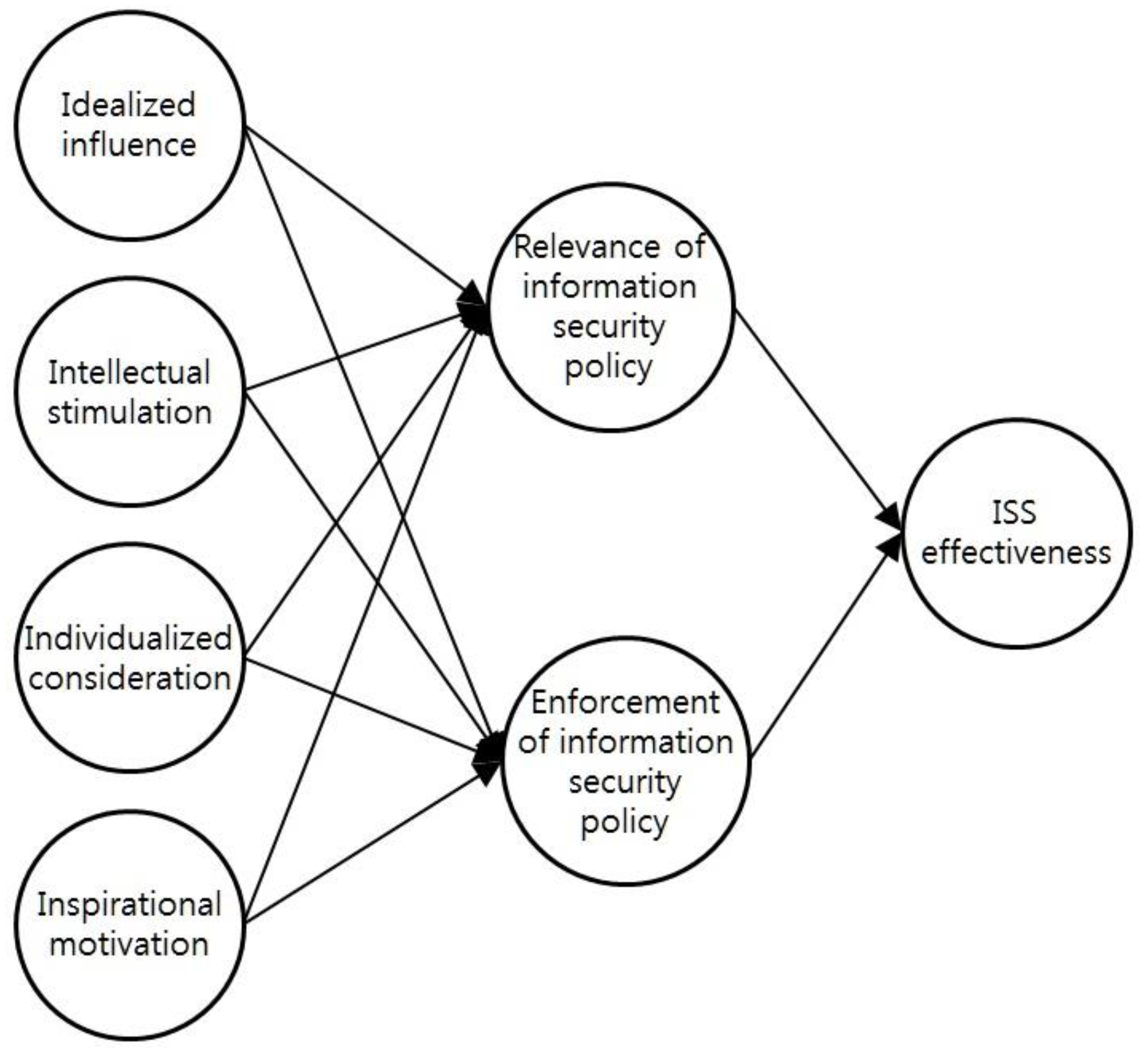
Sustainability Free Full Text Leadership Of Information Security Manager On The Effectiveness Of Information Systems Security For Secure Sustainable Puting Html
| Title: Sustainability Free Full Text Leadership Of Information Security Manager On The Effectiveness Of Information Systems Security For Secure Sustainable Puting Html |
| Format: PDF |
| Number of Pages: 193 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: January 2017 |
| File Size: 2.8mb |
| Read Sustainability Free Full Text Leadership Of Information Security Manager On The Effectiveness Of Information Systems Security For Secure Sustainable Puting Html |
 |
S Enisa Europa Eu Publications Railway Cybersecurity At Download Fullreport
| Title: S Enisa Europa Eu Publications Railway Cybersecurity At Download Fullreport |
| Format: PDF |
| Number of Pages: 300 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: August 2019 |
| File Size: 5mb |
| Read S Enisa Europa Eu Publications Railway Cybersecurity At Download Fullreport |
 |

Prepare Your Pany With Our Cyber Security Checklist Stanfield It
| Title: Prepare Your Pany With Our Cyber Security Checklist Stanfield It |
| Format: PDF |
| Number of Pages: 277 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: July 2018 |
| File Size: 1.4mb |
| Read Prepare Your Pany With Our Cyber Security Checklist Stanfield It |
 |

Pdf Cyber Security Management Model For Critical Infrastructure
| Title: Pdf Cyber Security Management Model For Critical Infrastructure |
| Format: eBook |
| Number of Pages: 273 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: April 2020 |
| File Size: 810kb |
| Read Pdf Cyber Security Management Model For Critical Infrastructure |
 |

The Definitive Cyber Security Guide For Small To Medium Businesses
| Title: The Definitive Cyber Security Guide For Small To Medium Businesses |
| Format: eBook |
| Number of Pages: 328 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: February 2021 |
| File Size: 2.8mb |
| Read The Definitive Cyber Security Guide For Small To Medium Businesses |
 |

Cyber Security Management Of Industrial Automation And Control Systems Iacs Asset Guardian Solutions Limited
| Title: Cyber Security Management Of Industrial Automation And Control Systems Iacs Asset Guardian Solutions Limited |
| Format: eBook |
| Number of Pages: 325 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: June 2018 |
| File Size: 3.4mb |
| Read Cyber Security Management Of Industrial Automation And Control Systems Iacs Asset Guardian Solutions Limited |
 |
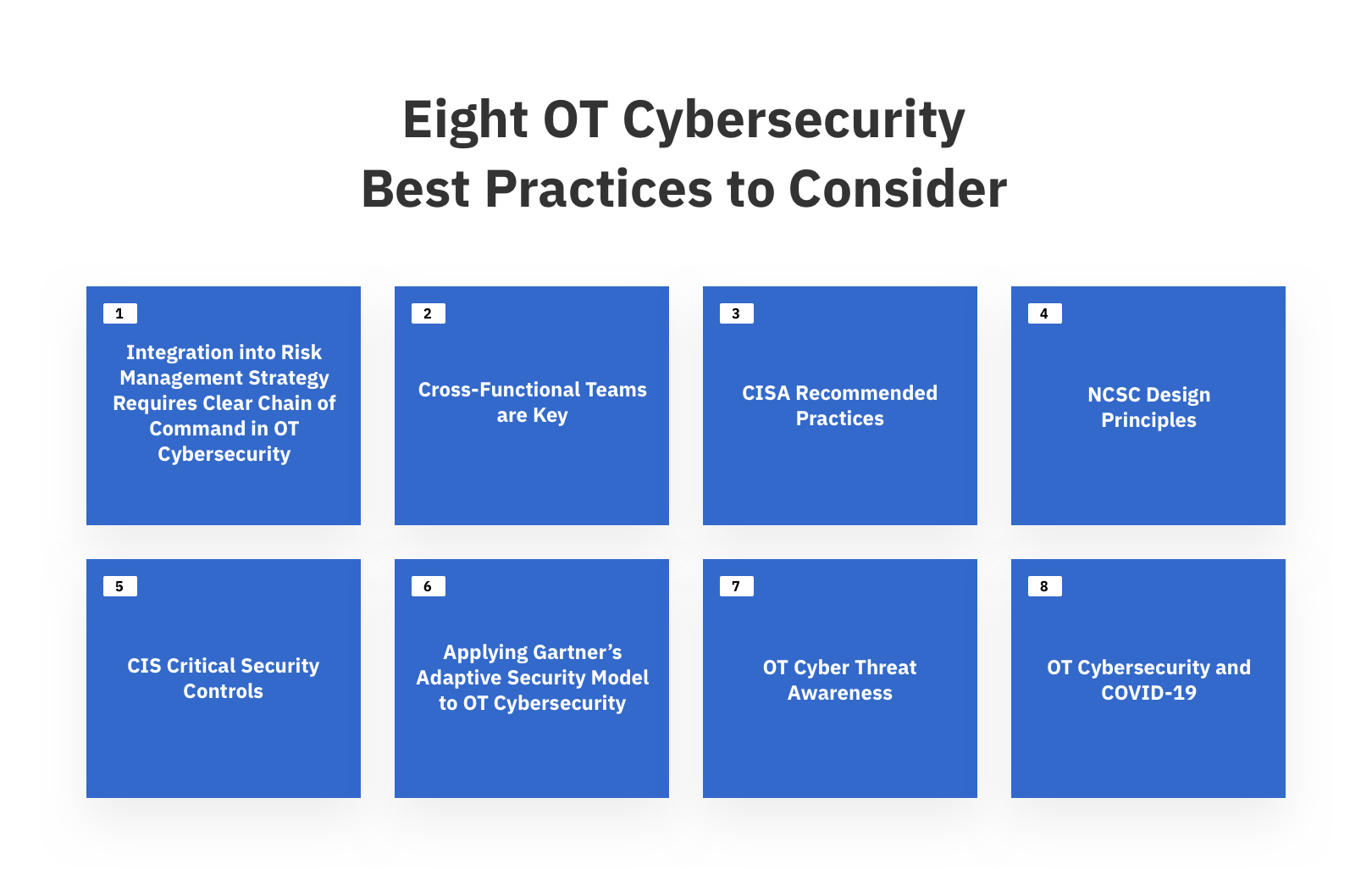
Cybersecurity Ot A Prehensive Guide
| Title: Cybersecurity Ot A Prehensive Guide |
| Format: ePub Book |
| Number of Pages: 183 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: June 2019 |
| File Size: 6mb |
| Read Cybersecurity Ot A Prehensive Guide |
 |

Pdf Information Security In An Anization
| Title: Pdf Information Security In An Anization |
| Format: eBook |
| Number of Pages: 145 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: November 2019 |
| File Size: 3.4mb |
| Read Pdf Information Security In An Anization |
 |
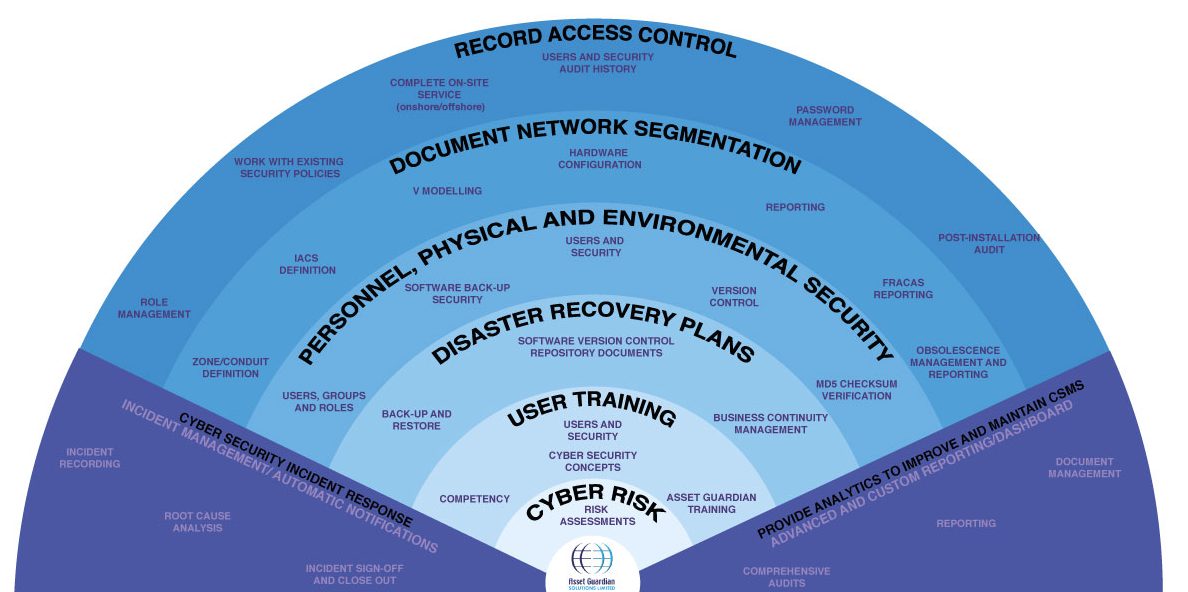
Cyber Security Management Of Industrial Automation And Control Systems Iacs Asset Guardian Solutions Limited
| Title: Cyber Security Management Of Industrial Automation And Control Systems Iacs Asset Guardian Solutions Limited |
| Format: PDF |
| Number of Pages: 209 pages Challenges Of Maintaining Information Security At A Remote Recovery Location |
| Publication Date: July 2017 |
| File Size: 5mb |
| Read Cyber Security Management Of Industrial Automation And Control Systems Iacs Asset Guardian Solutions Limited |
 |
Question Description Discuss the challenges of maintaining information security at a remote recovery location. Discuss the challenges of maintaining information security at a remote recovery location. Question DescriptionDiscuss the challenges of maintaining information security at a remote recovery locationI recommend your initial posting to be between 200-to-300 wordsposts must contain a properly formatted in-text citation and scholarly reference.
Here is all you need to read about challenges of maintaining information security at a remote recovery location Note that the requirement is to post your initial response no later than Sunday and you must post one additional post during the week. The replies to fellow students and to the professor should range between 100-to-150 words. I recommend your initial posting to be between 200-to-300 words. S enisa europa eu publications railway cybersecurity at download fullreport pdf information security in an anization pdf reviewing cyber security social engineering training and awareness programs pitfalls and ongoing issues cybersecurity ot a prehensive guide s sparta eu assets deliverables sparta d9 1 cybersecurity skills framework pu m12 pdf prepare your pany with our cyber security checklist stanfield it Discuss the challenges of maintaining information security at a remote recovery location.


0 Komentar